New MongoDB, MySQL, and PostgreSQL Protocol Dissectors
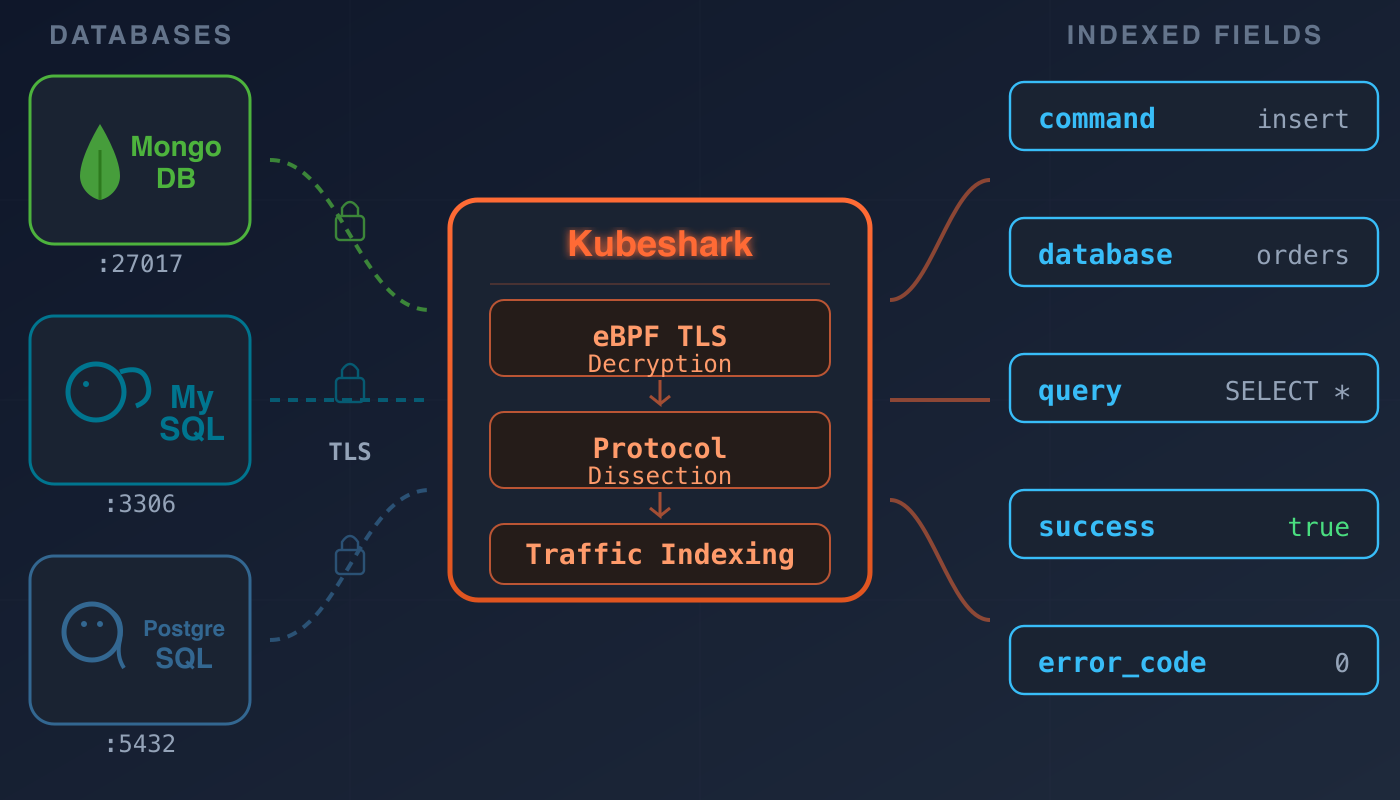
Kubeshark captures and indexes cluster-wide network traffic, making it queryable using network semantics (IPs, ports, L4 flows), Kubernetes semantics (pods, services, namespaces, labels), and API semantics (protocol-specific fields like HTTP methods, gRPC status codes, DNS question types, Redis commands, Kafka topics).
With the addition of MongoDB, MySQL, and PostgreSQL dissectors, the API semantics now extend to database wire protocols — command types (mongodb_command, mysql_command, postgresql_command), database names (mongodb_database, mysql_database, postgresql_database), collections and tables (mongodb_collection), SQL query text (mysql_query, postgresql_query), error codes (mongodb_error_code, mysql_error_code), success/failure status (mongodb_success, mysql_success, postgresql_success), and payload sizes (mongodb_total_size, mysql_total_size). These join the existing set of queryable dimensions, indexed and filterable in real time via KFL.
Database traffic runs over binary wire protocols on ports 27017, 3306, and 5432. From a network capture, it's opaque byte streams. Add TLS — which you should — and it's doubly so. These new dissectors parse the wire formats natively, with full eBPF-based TLS decryption.
The Dissectors
MongoDB
Parses both OP_MSG (MongoDB 3.6+) and legacy OP_QUERY operations with a built-in BSON decoder. Request/response pairs are matched via requestID correlation.
Every insert, find, aggregate, listCollections — with database name, collection, command, and full document body.

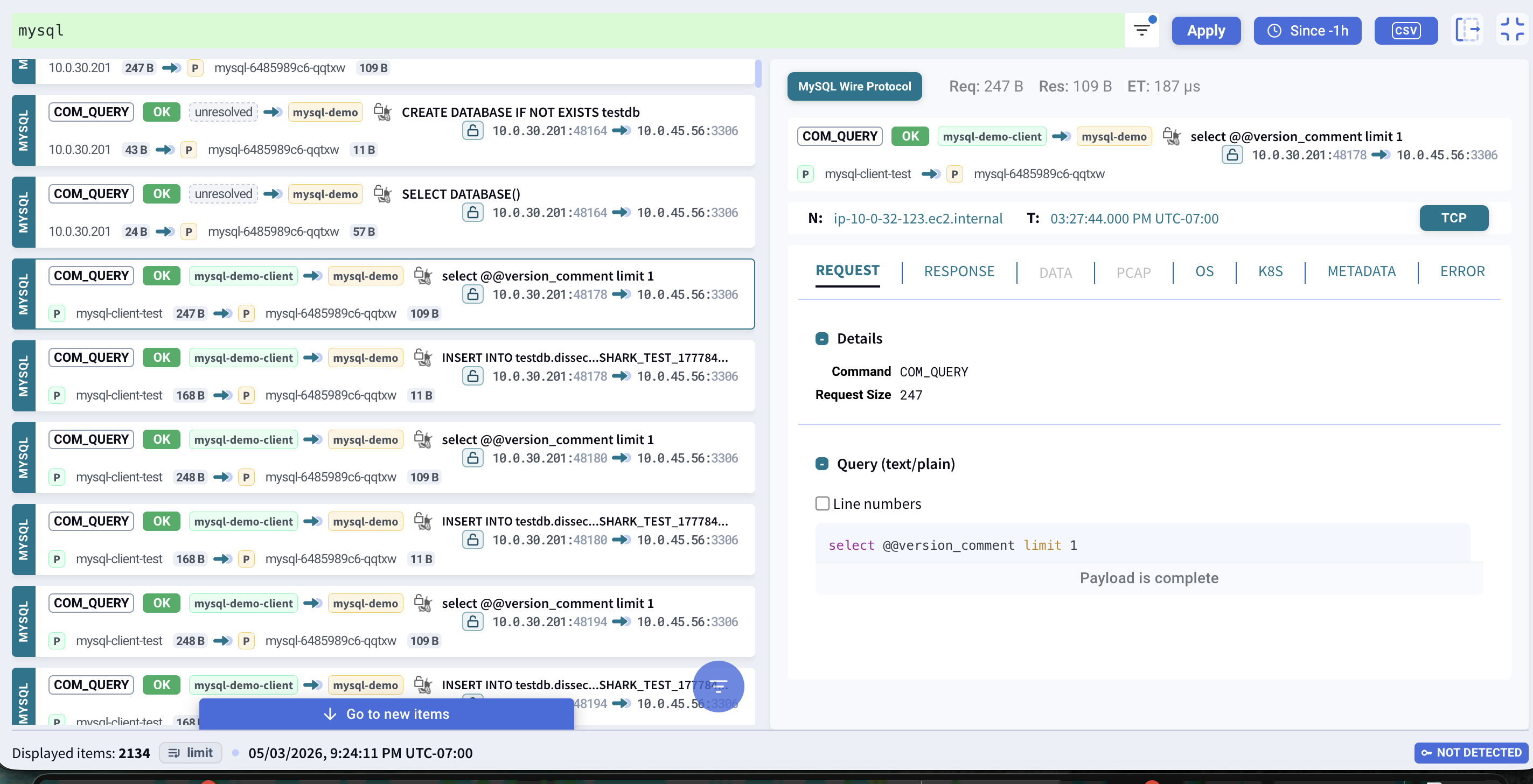
MySQL
Handles the full MySQL client/server protocol lifecycle: server handshake, authentication, and command phase. Parses COM_QUERY, COM_STMT_PREPARE, COM_INIT_DB, COM_STMT_EXECUTE, and COM_STMT_CLOSE. Multi-packet result sets (column definitions, row data, EOF markers) are consumed as single logical responses.
Covers MySQL 8.0 specifics: CLIENT_DEPRECATE_EOF (EOF packets replaced with OK-as-EOF) and CLIENT_QUERY_ATTRIBUTES (attribute bytes prefixed to SQL text).
Supports mid-stream connections — captures existing MySQL sessions that were already past handshake when Kubeshark started.
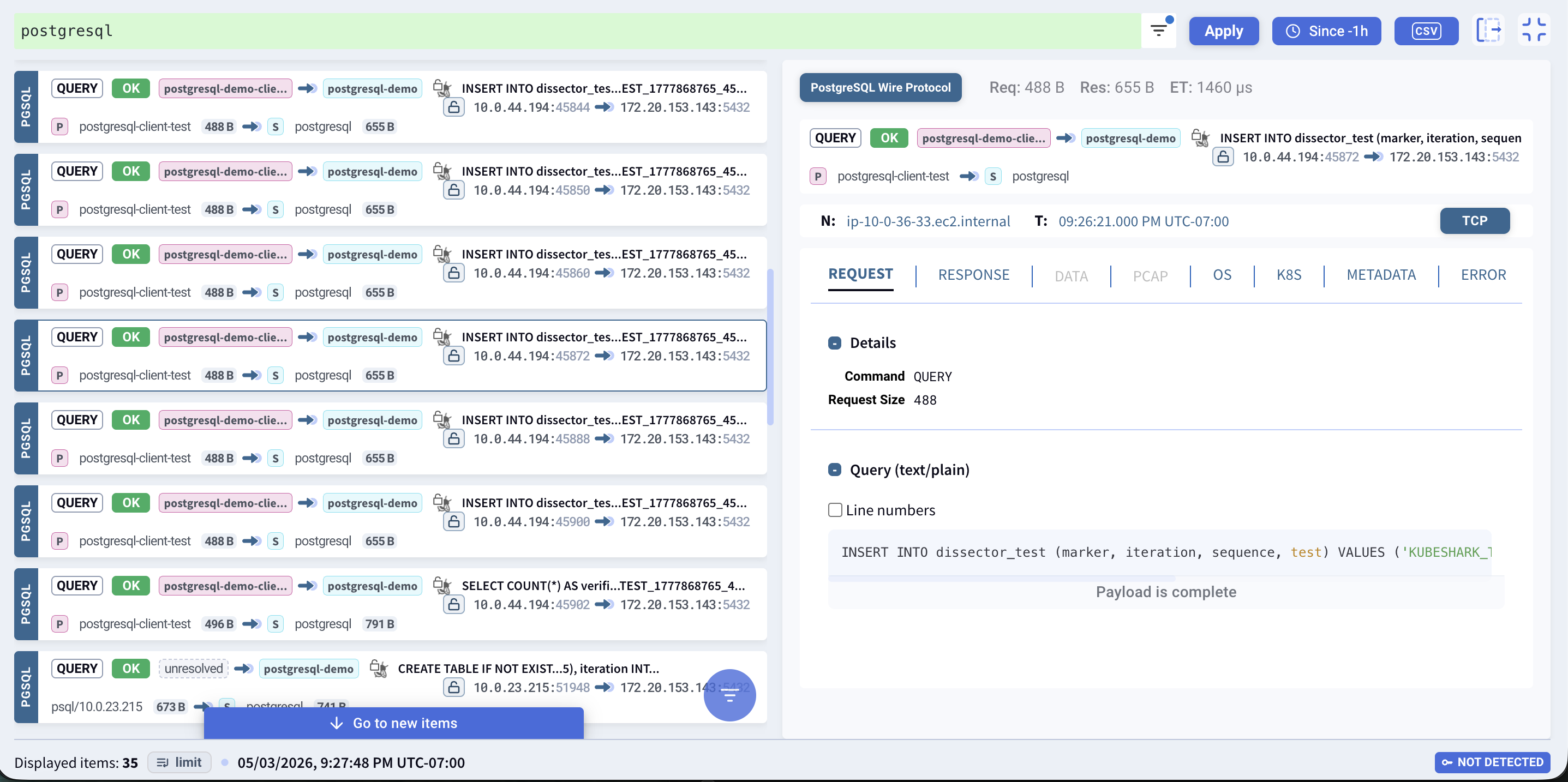
PostgreSQL
Parses the PostgreSQL wire protocol tagged message format: QUERY, PARSE, BIND, EXECUTE, DESCRIBE on the client side; RowDescription, DataRow, CommandComplete, ErrorResponse, ReadyForQuery on the server side.
SQL query text, database name, request/response sizes — all extracted and indexed.
TLS Decryption
All three dissectors integrate with Kubeshark's eBPF-based TLS interception. The hooks sit at the TLS library level (OpenSSL, Go crypto/tls, BoringSSL) — intercepting plaintext before encryption and after decryption. No certificates, no proxies, no sidecars.
Getting this right required solving a few non-obvious problems:
New syscall coverage. MongoDB 8.x uses recvmsg/sendmsg (via its Boost.Asio networking layer) instead of read/write. New eBPF tracepoints for sys_enter_{recvmsg,sendmsg,recvmmsg,sendmmsg,readv,writev} were added so SSL chunks from these syscall families get their file descriptors properly associated.
BSON false positives. The TLS-header heuristic — scanning the first 64 bytes for a TLS record pattern — was false-triggering on dense binary BSON payloads. Once tripped, the dissector classified the stream as "not my protocol" and never retried that connection. Fix: bypass the heuristic when the stream is already flagged as TLS-decrypted by the eBPF layer.
Supporting a new protocol is more than writing a parser. The entire pipeline — eBPF hooks, TLS interception, protocol dissection — has to work end-to-end.
KFL Filters
All three protocols have dedicated KFL variables for filtering by command, database, collection, error status, and payload size.
Live Demo
A live environment with MongoDB, MySQL, and PostgreSQL workloads is available — Kubeshark capturing and dissecting all traffic in real time, including TLS-encrypted connections.
Filters to try:
mongodb— insert, find, and aggregate operationsmysql— COM_QUERY with full SQL textpostgresql— queries with request/response payloads
Getting Started
Install Kubeshark
AI-Powered Analysis via MCP
Example queries:
"Show me all failed MongoDB operations in the users collection over the last 5 minutes."
"Which MySQL queries are exceeding 1 second?"
"What PostgreSQL databases are being accessed from the production namespace?"
Kubeshark — continuous cluster-wide traffic capture with protocol dissection for HTTP, gRPC, Redis, Kafka, MongoDB, MySQL, PostgreSQL, and more. eBPF-based TLS decryption, Kubernetes enrichment, AI-powered analysis via MCP. Get started →